Assumes fully configured public DNS or DDNS, a functional PFSense installation with existing valid wildcard SSL certificate available, and a basic webservice on a single internal server, such as the Apache default page as a placeholder until further services are added. Adjust hostnames, IPs, etc to suit the environment.
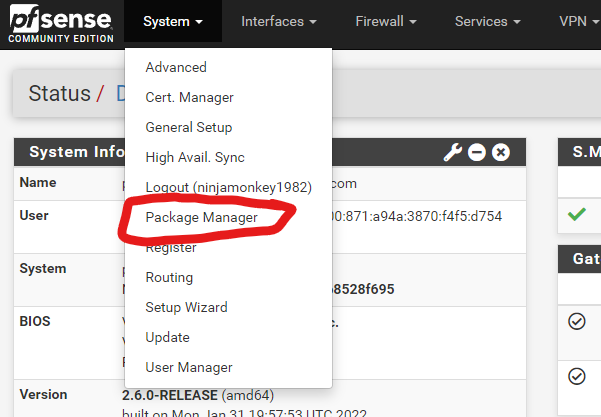
Go to System > Package Manager
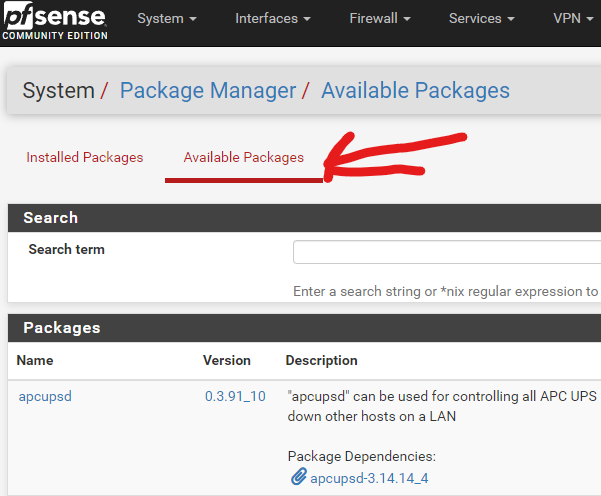
Select Available Packages
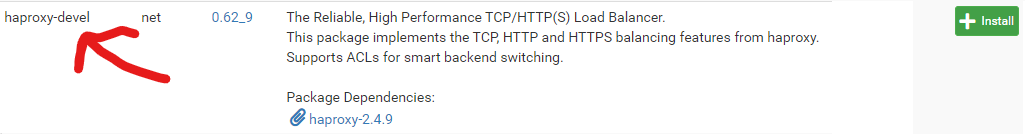
Find and install haproxy-devel
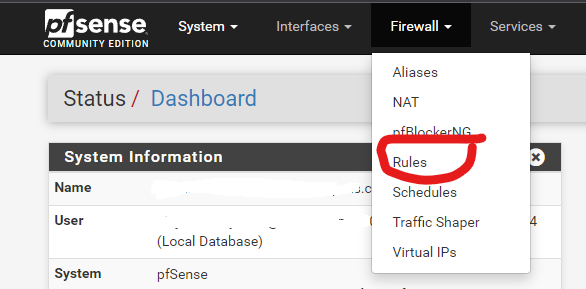
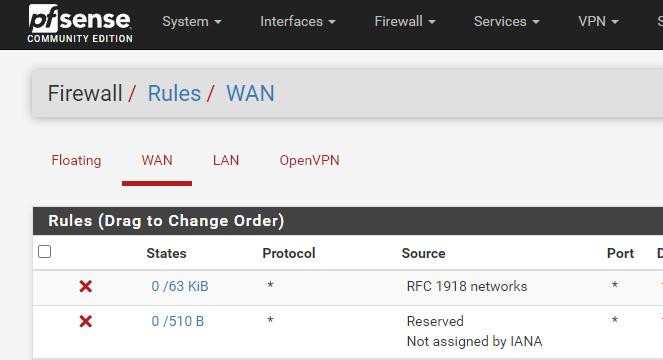
Go to Firewall > Rules
Select the WAN tab
Add the following two rules to the bottom of the list, nothing else should be using ports 80 and 443:
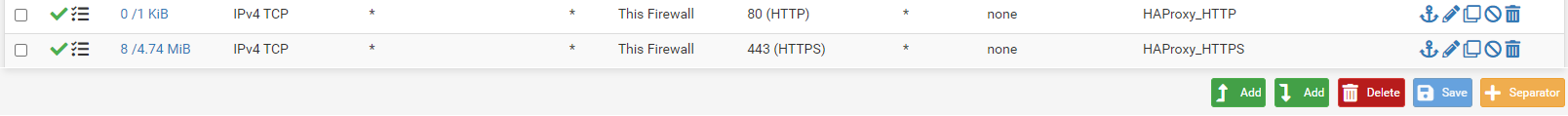
HTTP rule:
Create a duplicate rule, changing the port to 443 and the description for HTTPS
Enable the new rules.
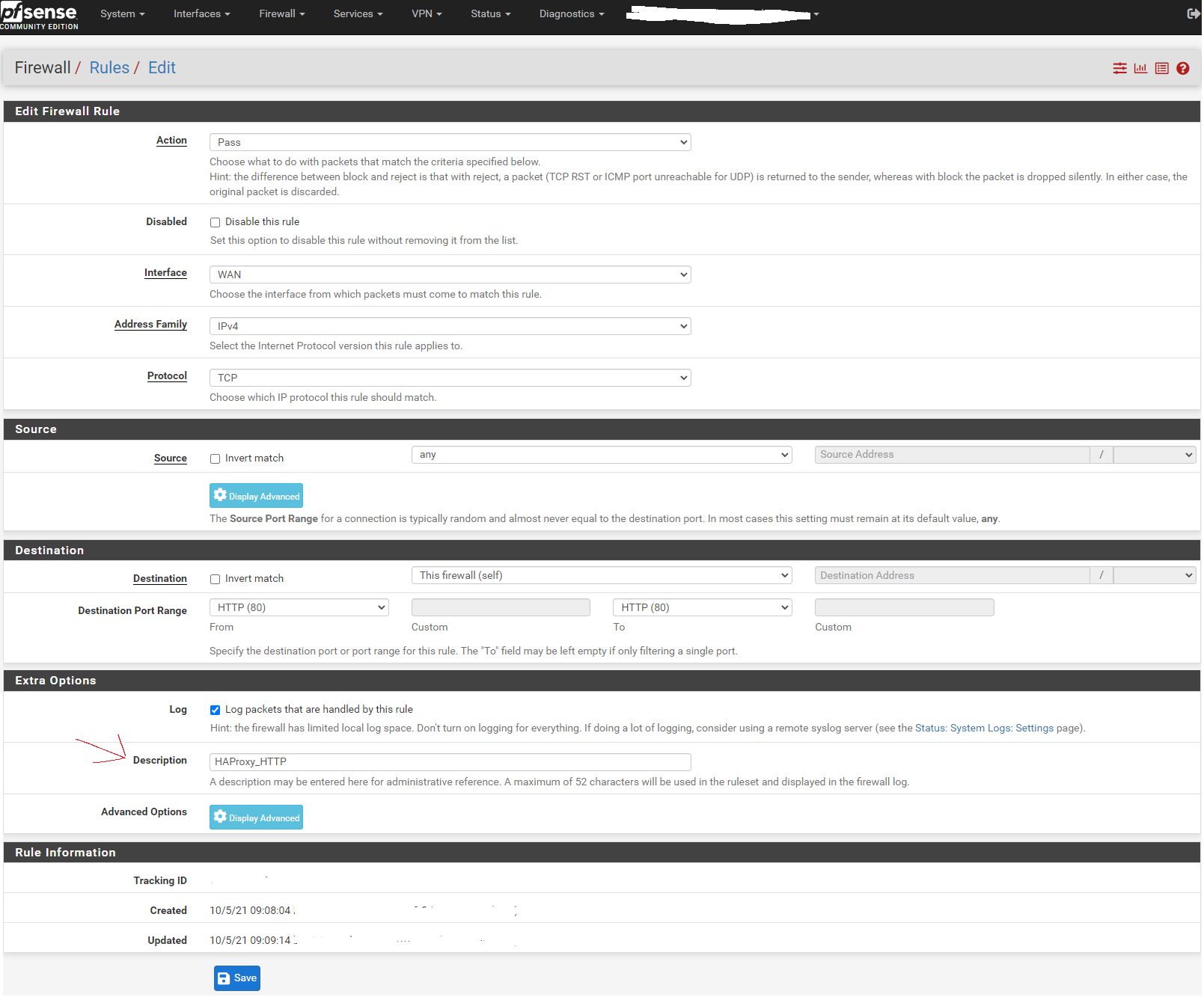
Go to Services > HAProxy
Leave the Settings tab alone for now and skip to the Backend tab:
Add a new backend for the webserver. Assumes server is listening on port 80. Enter the FQDN into the box titled Name, the click the down arrow in the Server list panel to add a server definition.
Enter the hostname only for the server in the Name box, enter the internal IP address of the server, and 80 for the Port. Leave the other settings alone.
In the Health checking section, set Health check method to none.
Scroll down, save, and apply changes when asked.
Now go to the Frontend tab. Click the button to add a new frontend.
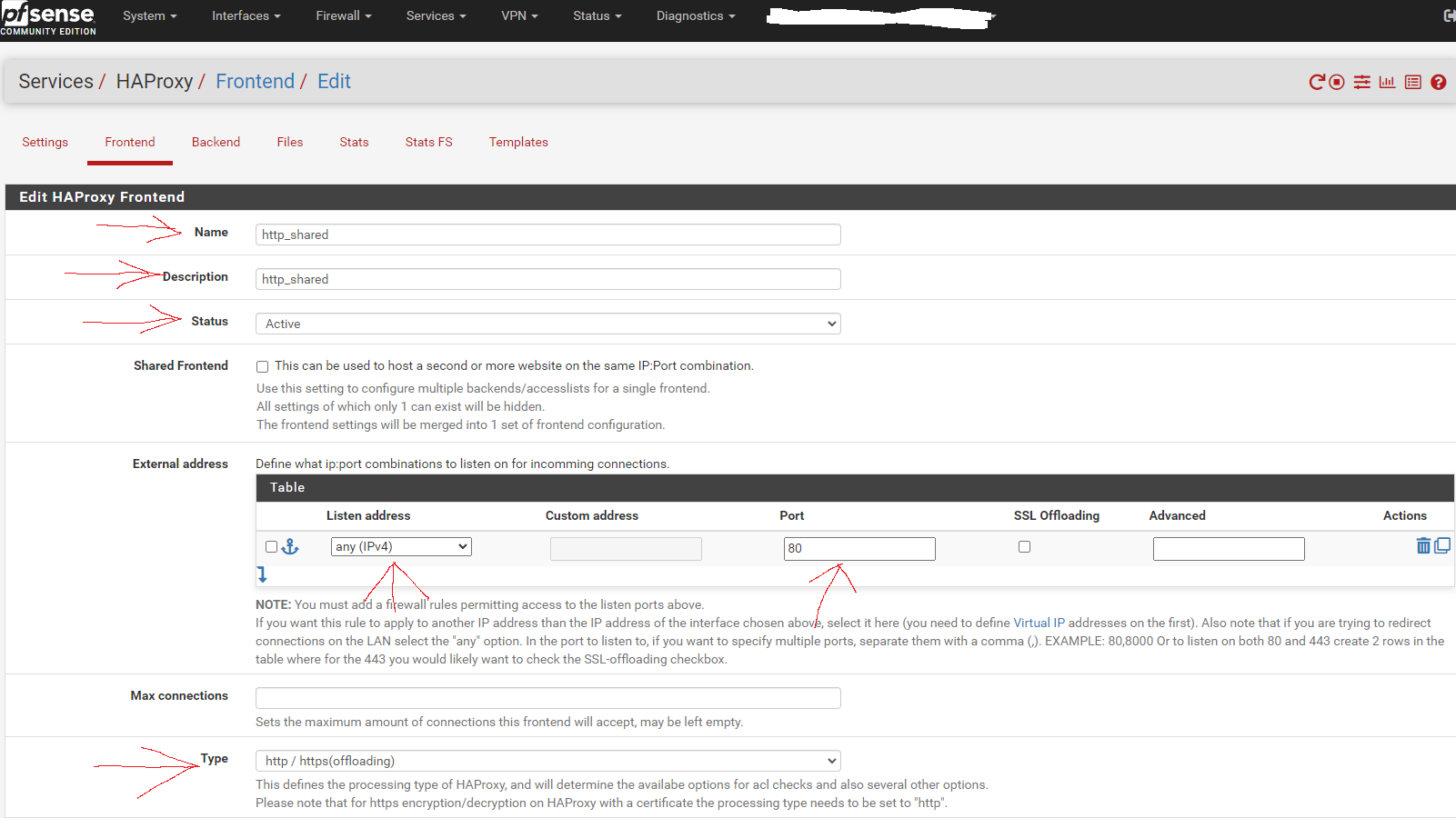
This shared http frontend will redirect all configured entries to their HTTPS equivalent and allow SSL offloading, as well as both internal and external access to the sites/services via URL.
Fill in the entries as shown in the screen capture below:
Scroll to the section titled "Default backend, access control lists and actions" and in the Action Control lists area click the down arrow to create a new acl for your server. Enter the hostname in the Name field, change the Expression to Host matches, and enter the FQDN of the website/service into the Value field.
Scroll down to the Actions area of the section and click the down arrow to create a new action. In the Action field, select http-request redirect, enter scheme https into the rule field, and enter the hostname into the Condition acl names field.
Scroll down and select None for the Default Backend.
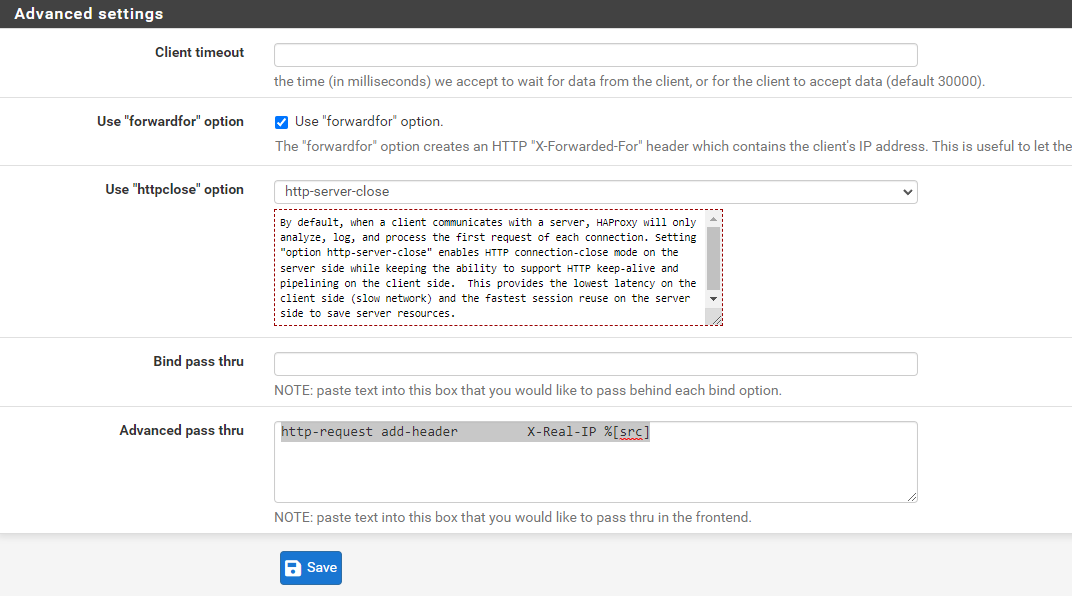
Scroll down to the Advanced settings section. Tick the Use "forwardfor" option box, select http-server-close for Use "httpclose" option, and add/copy-paste
http-request add-header X-Real-IP %[src]
to the Advanced pass thru text box.
Save and apply changes.
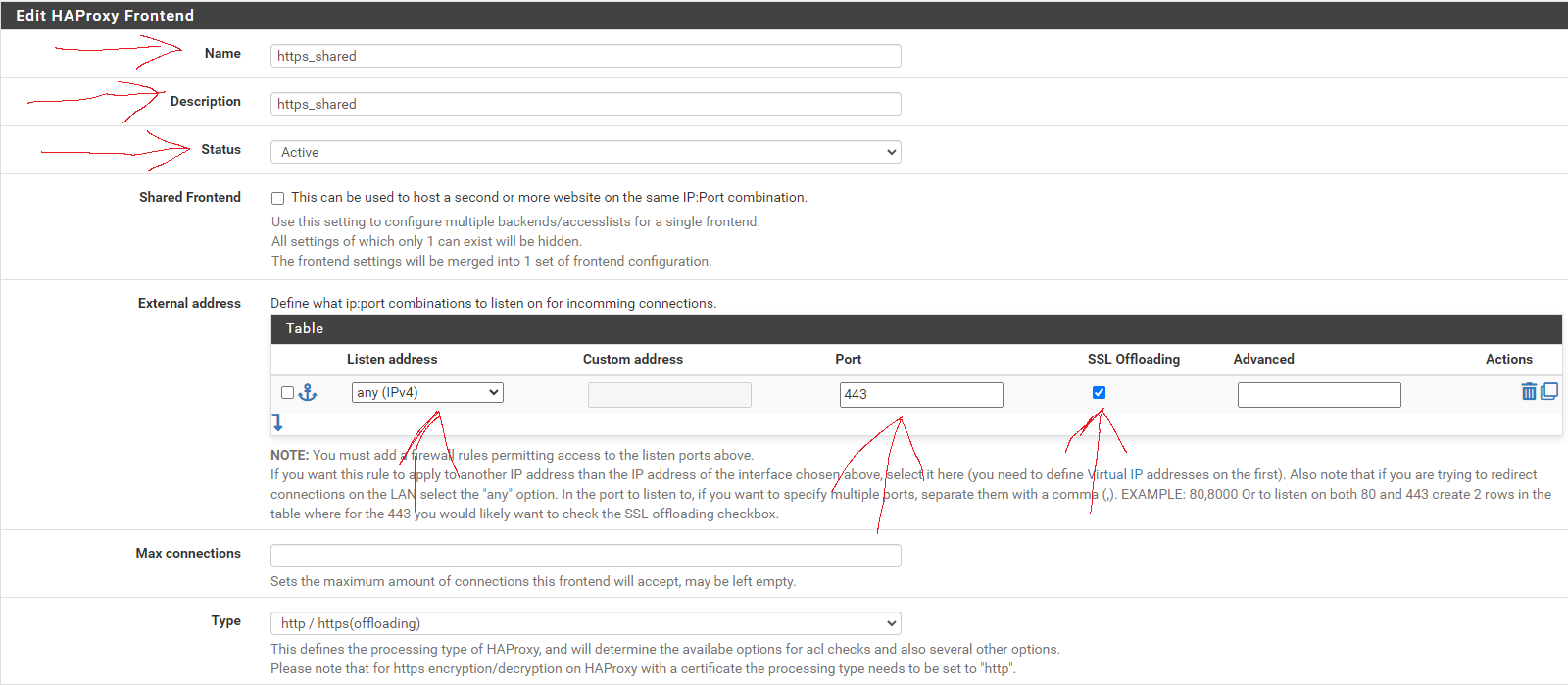
Click the button to add a new frontend.
Fill in the entries as shown in the screen capture below:
No entries are necessary in the Default backend, access control lists and actions section, just make sure to set the Default Backend to None.
As before, scroll down to the Advanced settings section, tick the Use "forwardfor" option box, select http-server-close for Use "httpclose" option, and add/copy-paste
http-request add-header X-Real-IP %[src]
to the Advanced pass thru text box.
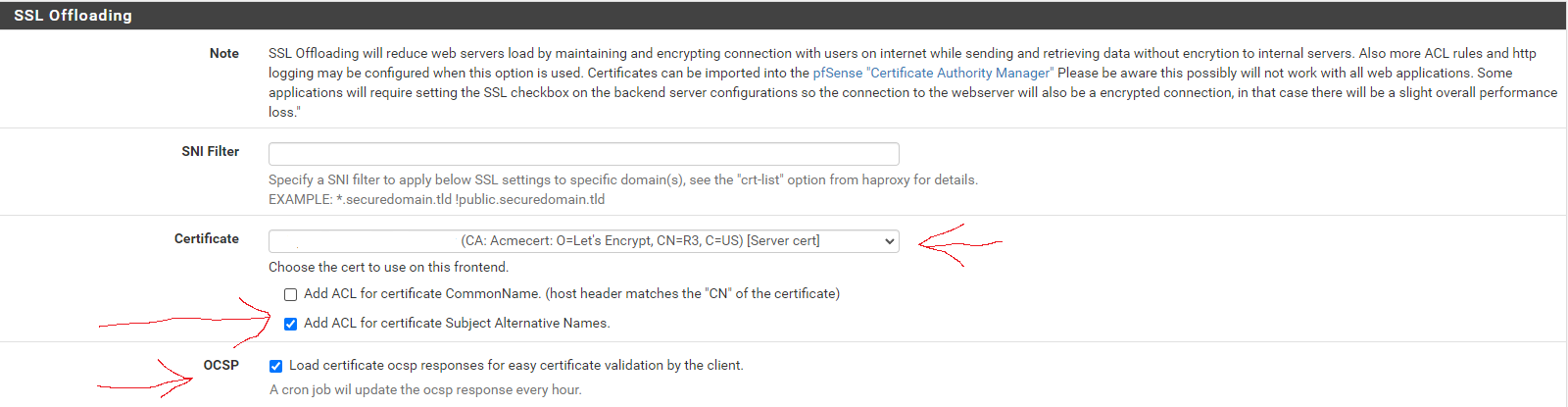
Next, scroll down to the SSL Offloading section. In the Certificate area, select the wildcard certificate for the domain and tick the box to Add ACL for certificate Subject Alternative Names.
In the OCSP area, tick the option box.
Save and apply changes.
This shared HTTPS frontend will provide SSL offloading for ALL HTTPS frontends using it as a shared frontend, while allowing other ACLs and actions to be assigned to individual sub frontends independent from each other, as well as give a visual list of frontends/services that's easier to read than a long list of ACLs.
Click the button to add a new frontend.
Fill out the fields as in the picture below. In the Name field, enter the hostname. In the Description field, enter the FQDN. Set the Status to active, tick the Shared Frontend box, and select https_shared - http as the Primary frontend.
Scroll to the section titled "Default backend, access control lists and actions" and in the Action Control lists area click the down arrow to create a new acl for your server. Enter the hostname in the Name field, change the Expression to Host matches, and enter the FQDN of the website/service into the Value field. In the Actions area, click the down arrow to create a new action. In the Action field, select Use Backend, select the backend you created earlier, and enter the hostname into the Condition acl names field. Scroll down and select None for the Default Backend.
Save and apply changes.
The website/service should now be available internally and externally at the configured URL, with SSL encryption, and automatic HTTP to HTTPS forwarding.